SENTINELONE SONICWALL INTEGRATION
Closing the gap on today’s advanced security attacks requires tight integration between security solutions to detect new and existing threats and to automatically respond at machine speed. Traditional antivirus cannot keep up with today’s fast-evolving threat landscape. The SentinelOne-SonicWall integration enables SentinelOne’s autonomous prevention, detection and response capabilities to extend far beyond traditional endpoints in protecting enterprise networks of the future.
SonicWall and SentinelOne Join Forces to Provide Best-in-class Automated Real-time Breach Detection, Prevention and Remediation
- Partnership further enhances SonicWall’s layered security strategy by providing automated deployment and enforcement for SentinelOne endpoints
- Combined enforced solution ensures automatic remediation of advanced threats leveraging artificial intelligence powered static and behavioral analysis
- Partnership enhances the SonicWall Capture Threat Network by adding shared threat intelligence
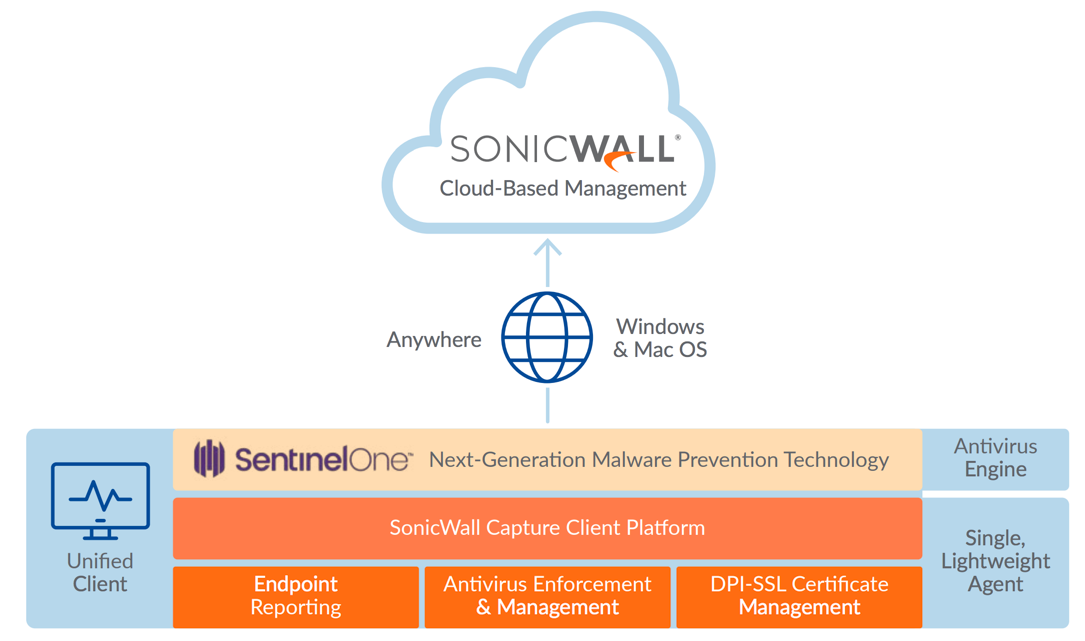
The ever-growing threat of ransomware and other malicious malware-based attacks has proven that client protection solutions cannot be measured based only on endpoint compliance. Traditional antivirus technology uses a long-embattled signature-based approach, which has failed to match the pace of emerging malware and evasion techniques. Those demand a different approach to client protection. Furthermore, with the proliferation of telecommuting, mobility and BYOD, there is a dire need to deliver consistent protection for endpoints anywhere. SonicWall Capture Client is a unified endpoint offering with multiple protection capabilities. With a next-generation malware protection engine powered by SentinelOne, Capture Client applies advanced threat protection techniques, such as machine learning and system rollback. Capture Client also leverages the deep inspection of encrypted TLS traffic (DPI-SSL) on SonicWall firewalls by installing and managing trusted TLS certificates. Capture Client co-exists with the SonicWall Content Filtering Client and the SonicWall Global VPN Client. Policies for all products can be managed from a single cloud-based management console. Capture Client can be easily added to any client deployed either through Microsoft Active Directory group policies or any other third-party software deployment techniques; or through the delivery of customized URLs where clients can download and silently self-install without any additional intervention. And, when integrated with SonicWall firewalls, Capture Client delivers a zero-touch silent experience for deployment on unprotected clients.
Key Benefits
- Continuous behavioral monitoring of the client helps create a complete profile of file activity, application and process activity, and network activity. This allows for protection against both file-based and fileless malware and delivers a 360-degree attack view with actionable intelligence relevant for investigations.
- Multiple layered, heuristic-based techniques for protection include cloud intelligence, advanced static analysis and dynamic behavioral protection. These helps protect against and remediate known and unknown malware.
- No need for regular scans or periodic updates enables the highest level of protection at all times without hampering user productivity.
- Unique rollback capabilities also support policies that not only remove the threat completely but also restore a targeted client to the state before the malware activity initiated. This eliminates the need for manual restoration in the case of ransomware and similar attacks.
- Cloud-based management console reduces the footprint and overhead of management. It also improves the ability to deploy and enforce endpoint protection, wherever the endpoint is.
- Integration with the SonicWall next-generation firewalls delivers zero-touch deployment and enhanced endpoint compliance. Plus it enables enforcement of deep packet inspection of encrypted traffic (DPI-SSL) by deploying trusted certificates to each endpoint.
- Centralized Management and Client Protection Reporting The SonicWall cloud-based management console functions as a single pane of glass to manage all client policies, including next-generation malware protection, DPI-SSL certificate management, content filtering and VPN.
- The management console is a multitenant cloud-based platform offered at no additional cost. It provides client protection reporting and policy management, with support for fine-grain access control policies. These allow managed service providers (MSPs) to manage and report on clients of multiple customers. At the same time, each of those customers can only manage and report on their own clients. It also functions as an investigative platform to help identify the root cause of detected malware threats and provide actionable intelligence about how to prevent these from recurring. For example, an administrator can easily view what applications are running on a client. That, in turn, can help identify machines that may be running vulnerable or unauthorized software.
Offerings and Platform Support
The SonicWall Capture Client is available in two offerings: SonicWall Capture Client Basic delivers all SonicWall next-generation malware protection and remediation features, along with DPI-SSL support capabilities. SonicWall Capture Client Advanced delivers everything listed above for Basic, plus advanced rollback capabilities. Both offerings are available for Windows 7 and higher, as well as for Mac OSX.
About SonicWall
SonicWall has been fighting the cybercriminal industry for over 25 years, defending small, medium size businesses and enterprises worldwide. Our combination of products and partners has enabled a real-time cyber defense solution tuned to the specific needs of the more than 500,000 businesses in over 150 countries, so you can do more business with less fear.
Autonomous Endpoint Protection That Saves You Time
The SentinelOne Endpoint Protection Platform unifies prevention, detection, and response in a single purpose-built agent powered by machine learning and automation. It provides prevention and detection of attacks across all major vectors, rapid elimination of threats with fully automated, policy-driven response capabilities, and complete visibility into the endpoint environment with full-context, real-time forensics.

